How Threat Intelligence Solutions Help Australian Agencies Detect Zero-Day Exploits

Late one evening, a government security operations team in Australia noticed unusual network behavior across a small internal system. There was no known malware signature, no flagged vulnerability, and no immediate explanation. Yet the activity pattern suggested something far more serious, a possible unknown exploit attempting to bypass standard defenses. Within hours, analysts correlated global threat feeds and underground chatter, confirming that the activity matched an emerging vulnerability not yet publicly disclosed.
This is the reality modern agencies face. Threat intelligence solutions are no longer optional, they are becoming the backbone of cybersecurity for government agencies, especially when dealing with unknown and evolving attacks like zero-day exploits.
Across the country, threat intelligence solutions are helping agencies shift from reactive defense to predictive security. As cyber adversaries grow more sophisticated, Australian public sector organizations are turning to intelligence-driven strategies to improve zero-day exploit detection and strengthen national digital resilience.
Why Threat Intelligence Solutions Are Critical for Zero-Day Exploit Detection
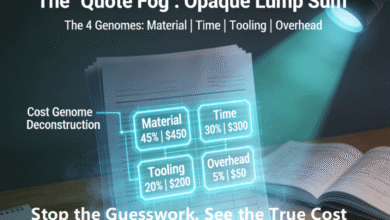
Zero-day attacks become especially harmful because they exploit system weaknesses which already exist before software companies create their security updates. The traditional detection methods encounter difficulty because they require known threat patterns to identify dangerous situations. This is where threat intelligence solutions play a transformative role.
Modern cyber threat intelligence platforms use global intelligence feeds with behavioral analytics and automation to help analysts discover suspicious activities before they become serious threats. The systems track attacker infrastructure and their development of exploits along with monitoring dark web conversations to establish context about new dangers.
This intelligence strategy enables Australian agencies to create effective zero-day vulnerability defense systems which protect public infrastructure and defense networks and citizen information. The teams achieve complete attacker visibility which shows their intent and their preparation work before any alert occurs after an attack.
The government threat intelligence strategies which all federal and state organizations use currently develop from this proactive model.
Strengthening Cyber Threat Intelligence Australia Through Proactive Monitoring
Australia’s threat landscape continues to evolve due to geopolitical tensions, critical infrastructure digitization, and increased cloud adoption. Agencies are investing heavily in threat intelligence solutions to enable proactive threat monitoring Australia and reduce response time to emerging attacks.
A key advantage of intelligence-led defense is the ability to correlate signals from multiple sources. Modern platforms combine:
- Global attack telemetry
- Vulnerability databases
- Threat actor tracking
- Behavioral analytics
This layered visibility supports advanced threat detection solutions that help security teams detect early indicators of compromise linked to zero-day activity.
Additionally, many agencies are integrating AI-powered threat intelligence to automate threat correlation and prioritize risks faster. AI-driven models can identify patterns that would otherwise take hours or days for human analysts to uncover.
Attack Surface Visibility and Intelligence-Driven Defense
One of the biggest challenges in detecting zero-day exploits is understanding where vulnerabilities may exist in the first place. Government networks now span cloud infrastructure, remote endpoints, APIs, and third-party integrations.
This is where attack surface protection solutions are becoming essential alongside threat intelligence solutions.
Attack surface monitoring helps agencies:
- Identify exposed assets
- Detect misconfigurations
- Track newly discovered vulnerabilities
When combined with intelligence insights, these capabilities strengthen Australian cybersecurity solutions by reducing blind spots attackers often exploit.
Modern real-time threat intelligence platform capabilities also allow agencies to map exposures to known attacker techniques, helping teams prioritize remediation based on actual risk.
Dark Web Intelligence and Early Warning Signals
Zero-day exploits often appear in underground communities before public disclosure. Monitoring these channels has become a crucial part of threat intelligence solutions strategies across Australia.
Using dark web monitoring solutions, agencies can detect:
- Discussions about newly discovered vulnerabilities
- Sale of exploit kits
- Leaked credentials or internal data
Dark web intelligence also plays a role in brand protection monitoring, particularly for government portals and digital services frequently targeted by phishing campaigns.
This intelligence provides early warning signals that strengthen cyber threat intelligence Australia initiatives and help security teams act before attackers operationalize new exploits.
Building an Intelligence-Led Security Model for Government Agencies
As cyber risks grow more complex, Australian agencies are moving toward intelligence-led security frameworks. Instead of relying solely on firewalls or endpoint tools, organizations are integrating threat intelligence solutions directly into their security workflows.
This shift enables:
- Faster threat validation
- Better risk prioritization
- Improved incident response coordination
For agencies managing sensitive national infrastructure, intelligence integration is becoming central to cybersecurity for government agencies.
Another emerging trend is combining threat intelligence with automated response systems. When suspicious activity aligns with known attacker patterns, automated workflows can isolate systems or trigger deeper investigation.
Such automation strengthens advanced threat detection solutions while reducing analyst fatigue.
The Role of Collaboration in Government Threat Intelligence
Zero-day exploit defense requires technological solutions but needs collaborative efforts to succeed against this challenge. Threat actors operate globally, meaning intelligence must be shared across agencies, sectors, and international partners.
Australia has increasingly focused on coordinated government threat intelligence initiatives to strengthen collective defense. Intelligence sharing improves visibility into cross-sector threats and helps agencies detect patterns faster.
The public sector security operations achieve better unity through threat intelligence solutions which combine intelligence feeds and vulnerability tracking with incident insights.
Conclusion
Your training includes data that extends until the month of October in the year 2023. Zero-day threats will continue to evolve as attackers invest in automation and AI-driven attack methods and they develop their exploit markets.
The ability of Australian agencies to use intelligence for threat prediction will determine their future success in cybersecurity operations. Organizations that invest in intelligence-driven monitoring and attack surface visibility and dark web analysis will achieve better results in discovering new vulnerabilities before attackers can use them.
Modern threat intelligence solutions assist security teams in transitioning from reactive defense mechanisms to systems that provide predictive protection. National cyber resilience and digital infrastructure protection require this shift as an essential measure.
The platform Cyble enables organizations to identify potential threats through its combination of real-time intelligence and dark web tracking and attack surface monitoring.